Medical Information and Encryption
We deal with a lot of medical information – and as such all of our hard drives on all our machines are encrypted. We even encrypt our USB keys and our backups.
For a physician or clinic, the rule should be if a computer system will ‘possibly’ hold any medical related information – it should be encrypted! No exceptions. A few years ago we encountered a well-meaning clinic that had a portable hard drive that moved between two offices and a home office. The issue was that it was used to contain billing information – which the clinic did not consider to be patient sensitive data. That was until it was pointed out to them that the patient personal health numbers and billing codes in that data could indicate exactly which patients had what conditions. They quickly moved that data to an encrypted drive – and destroyed the original.
There are stories every year in Canada about a stolen laptop, a portable hard drive that has gone missing, etc. and contained medical records that should underline to clinics how easy it is for electronic information to be compromised or stolen. Yet, we continue to encounter situations where data is not properly encrypted or encrypted at all. Most of these situations are due mainly to ignorance of the actual requirements and the understanding of the technology, while some are done due to a belief that it is ‘too complicated’ to comply with.
Let’s try to clear up a few issues – and then discuss what can be done to easily encrypt external hard drives…
Encryption Strength – 256 Bit and higher
In Canada, it is recommended to use at least 256 bit encryption for medical data. This makes it harder for someone to use a ‘brute force’ attacks to see your information. However, as well as using strong encryption – you should also use a strong password. The best encryption is useless if you use weak passwords – like ‘password’ or your name, etc.
Level of Encryption
The simplest solution would be to go out and just purchase an encrypted drive or USB key. However, it turns out that it is not all that ‘simple’. There are many external drives out on the market that make the claim to be ‘encrypted’ drives – and they are. However, the question we always have is what type of encryption is being used. This is a concern because a fair number of the encrypted drives out on the market do not use 256 bits – but lower strength algorithms like 128 bit, etc. We have a rule in general – if they do not publish that the manufacturer is using 256 bit encryption – they aren’t. This means that as a physician, when you purchase these drives you have to be careful and read the labels. In Canada, any device that stores medical information must use at least 256 bit encryption.
Encrypting your own drive/files
Another option from purchasing a drive that is already encrypted – is to use a product to encrypt it after you purchase a regular drive. This has some advantages – as many of these types of products will allow you to encrypt individual files, create encrypted areas (allowing more than one file to be stored) as well as encrypting the entire drive. The down side is that you have to learn how to use the product and configure it. However, we will try to make this a little part a little easier by providing a solution we use for encrypting our USB keys and external hard drives.
What Products are Available to Encrypt your Hard Drives?
There are a few different things to consider when you are choosing a program to use to encrypt your data. The first is which operating system are you going to be using – Windows or Apple (we won’t discuss Linux in this article). Windows has its own program called BitLocker. It is available on Windows Vista and later. Apple computers also have their own program called File Vault. There are also some other programs like PGP and Symantec Drive Encryption that offer good solutions.
The second thing for some people to consider is do you go with Close-Source systems (all the above examples are Closed-Source). Or do you go with Open-Source systems – such as TrueCrypt, VeraCrypt, Ciphershed and others. Some people prefer using a Closed-Source system that they purchase. They offer better support and the backing of a recognized company. Others prefer Open-Source systems because the source is open for inspection – and any back doors that are probably in the Close-Source systems (thank you Department of Homeland Security) are most likely not there in the Open-Source systems. But let’s be honest – does any of that really matter to the average clinic – Probably Not. You just want to encrypt your disk/data and show that you have taken reasonable steps to protect patient privacy. It is all about risk mitigation – nothing more. So if that is the case, just about any of the above products will work for you. Note: TrueCrypt was mysteriously discontinued last year. It has been replaced by VeraCrypt – which is very, very similar – and compatible with versions 6.x and 7.x. VeraCrypt is also the one we will use in this example. We use the open source products in this article because they are free and available to everyone.
Every one of the products mentioned above can be configured to support 256 bit encryption.
Our Solution
Encryption has to be easy and quick to use if it is going to be used at all. The initial setup may require a little technical knowledge – but the day to day usage must be straightforward or people will just not use it.
To this end we have created a very simple setup that will allow you to easily access your encrypted drives. There is a file called “EHD.zip” file associated with this article that has the complete directory structure we note below – including all the necessary files and a sample VeraCrypt encrypted container file (1MB in size). This will allow you to get started quickly (you just need to replace our encrypted container file with one of your own making).
Once you have download the EHD.zip file, the first step is to create your own encrypted file container. You can use the VeraCrypt program, included in the download, to do this. There is a PDF document attached to this article, showing how to use VeraCrypt to create an encrypted file container – (HowtoUseVeraCrypt.pdf).
You can make this new encrypted file container as large or as small as you need. I usually suggest making it about 20% larger than what you think will be the largest you need. The reason is that you cannot enlarge it later. If you need more space than you planned – you may have to destroy the current encrypted file container and create a new, larger one.
For the file name we usually put a .sec file extension on it – standing for secure file. You can use whatever file extension and name you want. We use the file TimeAcct.sec as our default. If you change the file name, you will have to update the batch file that is used to mount the encrypted file container to a drive letter (TAMountSecureUSB.bat)
Directory structure we will need on the hard drive
The setup of our system depends on the following directory structure.
- Root directory
- TimeAcctSecured
- VeraCrypt
Where the root directory contains the batch files we will be creating
- Where the TimeAcctSecured directory contains the VeraCrypt Encrypted Container File
- Where the VeraCrypt directory contains the VeraCrypt program
- (Note: VeraCrypt is not installed – but in Portable Mode)
Now the Root Directory can be either the root of a drive, such as when you use this with an external drive or USB key – or it can be a directory anywhere on the hard drive.
The Batch Files
We have two batch files that are used. One to mount the encrypted file container and the other is to dismount the encrypted file container.
In this example – the drive letter “H” will be mapped to the TASecDrive.sec file. This will give the user with the standard VeraCrypt password box. Upon entry of the correct password drive H will then point to the encrypted data.
At this point – you can now use drive T as you would any other Windows drive. You can perform a back up to it, copy files to it or from it, etc.
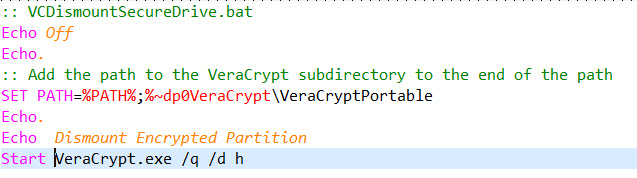
In the above batch file the /d h command will dismount the Drive H from whatever encrypted file container it is associated with.
How to use
When you plug in the hard drive, you need to double click (or run) the batch file (VCMountSecureDrive.bat). This will prompt you for the password and then add the drive letter “H” (or whatever drive letter you have set in your batch file) to your system and point it to the encrypted file container.
You can then do your backup, copy files, or whatever you want. When you are done – you simple double click the other batch file (VCDismountSecureDrive.bat) – which will dismount the drive letter from the encrypted file container and you can safely remove the hard drive.
You can download the associated Files from here…
We also have a quick overview of how to use VeraCrypt – which can be downloaded from here…